cybersecurity
27 articles

The Hidden Risk Threatening the Cold Chain: Cybersecurity Vulnerabilities in Control Systems
The Hidden Risk Threatening the Cold Chain: Cybersecurity Vulnerabilities in Control Systems

Cyber Crime Gangs Infiltrate Trucking Companies to Steal Shipments
Cyber Crime Gangs Infiltrate Trucking Companies to Steal Shipments

As Logistics Companies Accelerate Technology Investment in 2026, Cybersecurity Falls Behind
As Logistics Companies Accelerate Technology Investment in 2026, Cybersecurity Falls Behind

Suspect Arrested in UK During Probe into Cyberattack on European Airports
Suspect Arrested in UK During Probe into Cyberattack on European Airports

ISN Enhances Third-Party Cybersecurity Oversight Capabilities
ISN Enhances Third-Party Cybersecurity Oversight Capabilities

Coordinated Prevention Essential Against Rising Freight Fraud
Coordinated Prevention Essential Against Rising Freight Fraud

Cydome: Free Tool for Cyber Incident Reporting
Cydome: Free Tool for Cyber Incident Reporting

U.S. Coast Guard Cybersecurity Rule Enters Into Force
U.S. Coast Guard Cybersecurity Rule Enters Into Force

Cyberattack on Supplier Leaves Whole Foods Shelves Empty
Cyberattack on Supplier Leaves Whole Foods Shelves Empty

Cyber Attack Leaves Whole Foods Shelves Empty
Cyber Attack Leaves Whole Foods Shelves Empty

Marks & Spencer: Cyberattack Could Cost Up to £300 Million
Marks & Spencer: Cyberattack Could Cost Up to £300 Million
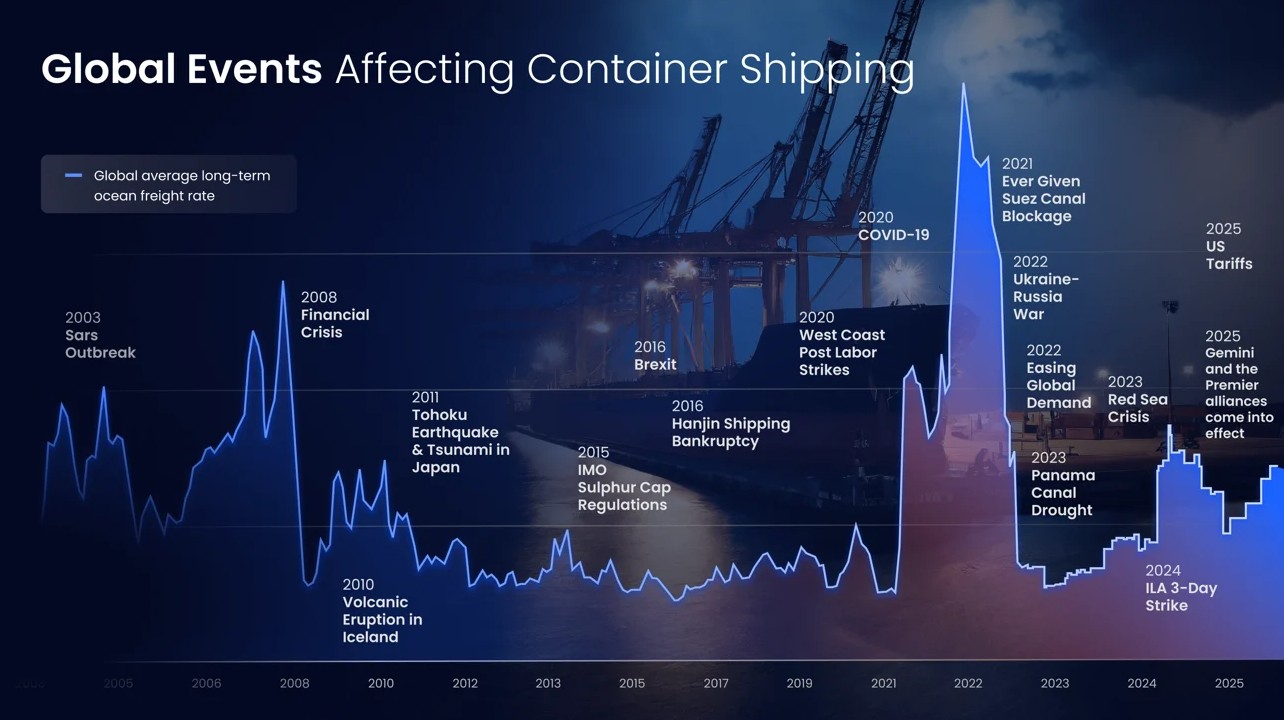
Supply Chain Risks and Anti-Fragility Strategy for 2025
Supply Chain Risks and Anti-Fragility Strategy for 2025

Ransom Payments in Maritime Sector: 7% of Companies Paid Ransoms in the Last 12 Months
Ransom Payments in Maritime Sector: 7% of Companies Paid Ransoms in the Last 12 Months

ERP Downtime Could Cost UK E-Commerce Firms More Than £26,000 a Day
ERP Downtime Could Cost UK E-Commerce Firms More Than £26,000 a Day
Fleet Cybersecurity Risk Mitigation Strategies
Fleet Cybersecurity Risk Mitigation Strategies

U.S. Supply Chain Chart New Course: First U.S. Quadrennial Supply Chain Review
U.S. Supply Chain Chart New Course: First U.S. Quadrennial Supply Chain Review
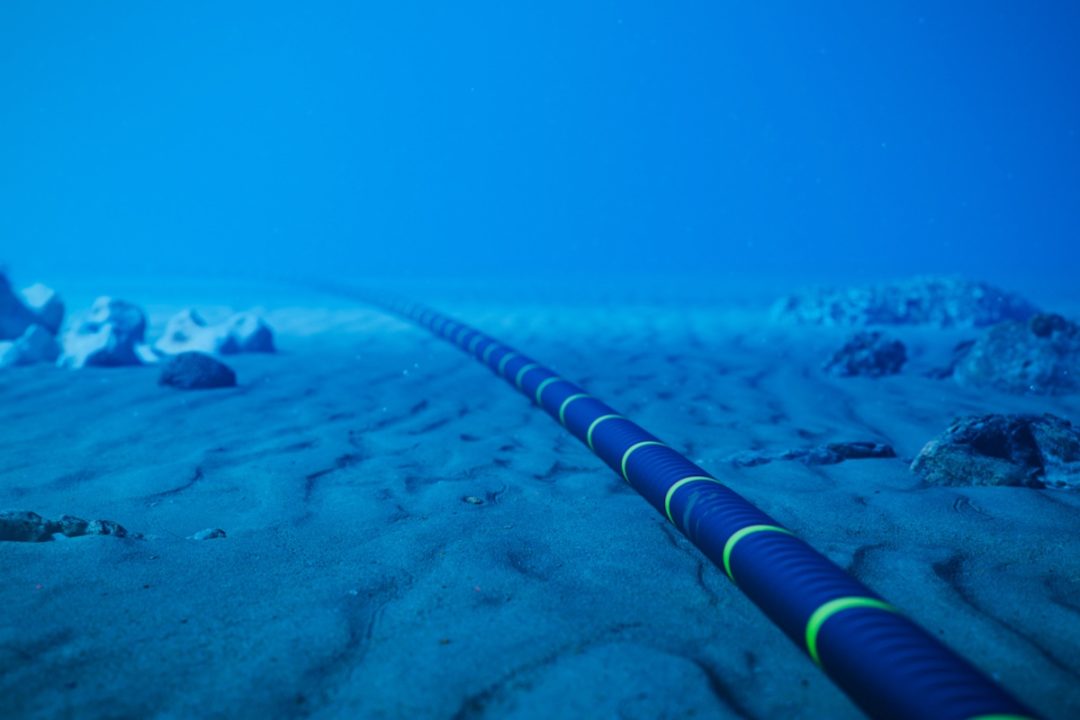
Chinese Carrier Detained on Suspicion of Sabotaging Telecom Lines in Baltic Sea
Chinese Carrier Detained on Suspicion of Sabotaging Telecom Lines in Baltic Sea
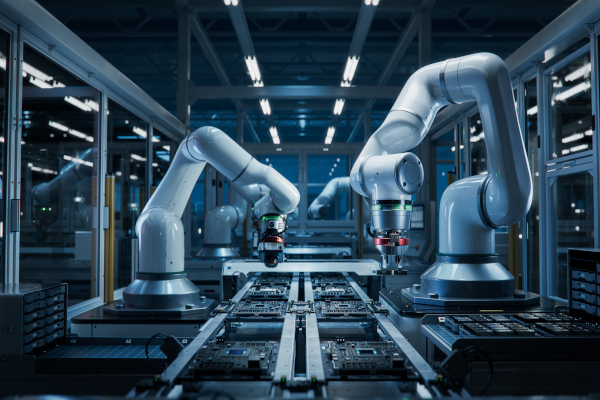
Manufacturers Struggle with IT Skills Gap and Cybersecurity Challenges
Manufacturers Struggle with IT Skills Gap and Cybersecurity Challenges
Lloyd's Register Releases Digital Maturity Assessment for Maritime Sector
Lloyd's Register Releases Digital Maturity Assessment for Maritime Sector

Failure to Update SAP Systems Creates Major Risk in Manufacturing Sector
Failure to Update SAP Systems Creates Major Risk in Manufacturing Sector

U.S. Congress Recommendation: Airlines Should Be Prepared for Future Disruptions
U.S. Congress Recommendation: Airlines Should Be Prepared for Future Disruptions

CrowdStrike's Ripple Effects on Supply Chains
CrowdStrike's Ripple Effects on Supply Chains
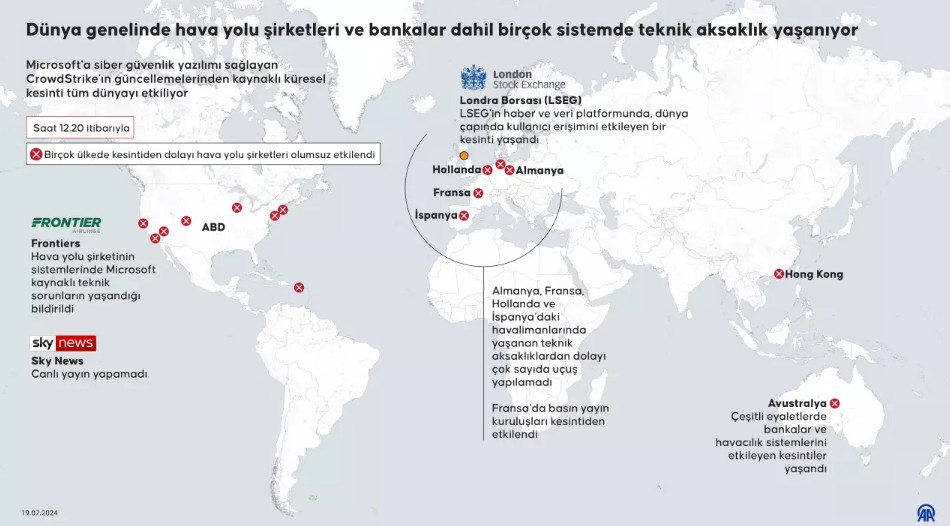
Global Software Outage: Microsoft and CrowdStrike System Failure Rattles the World
Global Software Outage: Microsoft and CrowdStrike System Failure Rattles the World
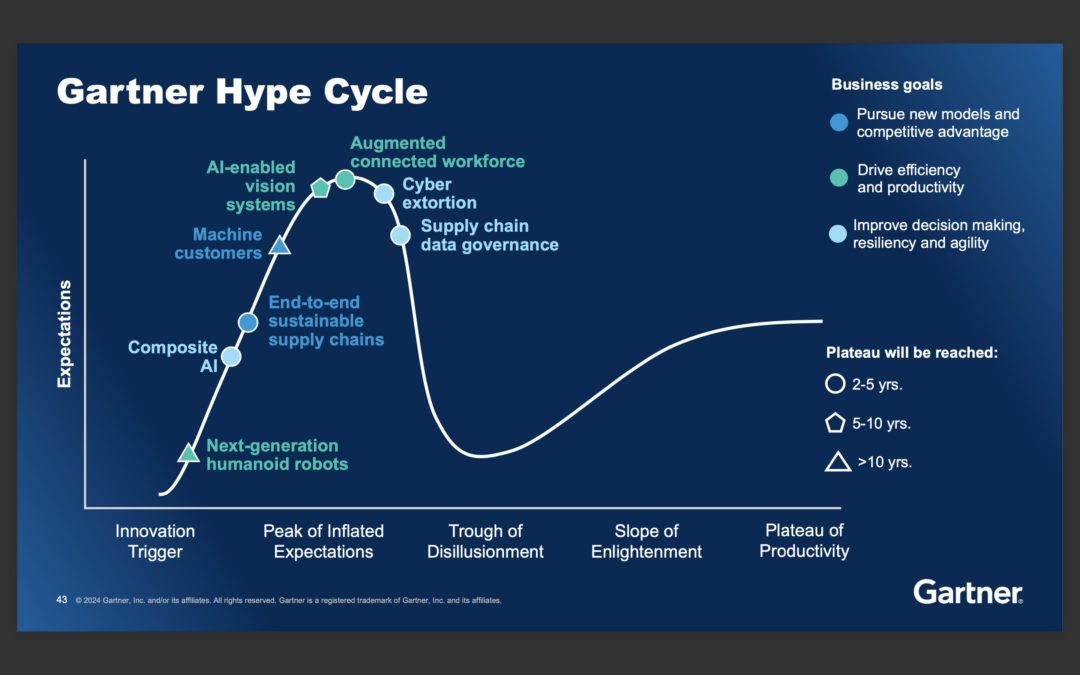
Leading Trends in Supply Chain Digital Transformation
Leading Trends in Supply Chain Digital Transformation

Why Do Cybercriminals Target the Transportation Industry?
Why Do Cybercriminals Target the Transportation Industry?

Digital Transformation in Shipping: The Rise of Electronic Bills of Lading
Digital Transformation in Shipping: The Rise of Electronic Bills of Lading
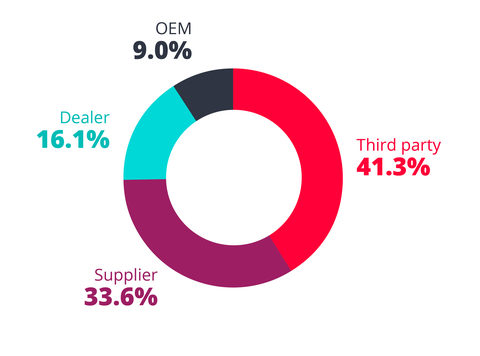
Hackers Target Third-Party Suppliers in Automakers' Supply Chains
Hackers Target Third-Party Suppliers in Automakers' Supply Chains